The Risk of Using Legacy Medical Devices with Outdated Software
The healthcare industry is a prime target for cyberattacks and has been for years. The main reason being that personal health information is worth more on the black market compared to any other data. These cyberattacks have disrupted operations within hospitals, resulting in patient safety issues and more.
Due to these attacks, the U.S. Cybersecurity and Infrastructure Security Agency issued several safety alerts specifically regarding medical devices. Here’s why.
The problems caused by outdated medical device software
We all know how fast technology changes, improves and adapts. For example, just look at how often programs on your computer or your smartphone are updated. What’s updated even more often, though, are your security programs like antivirus software, anti-malware software and firewalls. These programs are updated regularly to combat the newest viruses and other online threats.
Knowing that software is constantly evolving, what can happen when it is no longer updated? Unfortunately, the software becomes an easy target for hackers, which is why medical devices can be vulnerable.
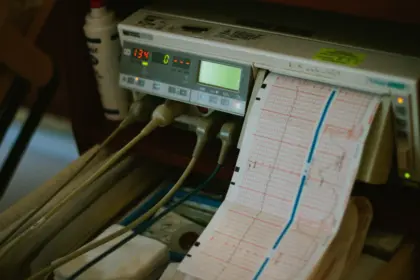
Legacy medical devices contain outdated software because they do not receive manufacturer support for patches or updates, making them very vulnerable to cyber attacks. Some medical hardware devices can be used for a long period of time, some up to 30 years. Although the device itself works fine, software made 30 years ago will be quite different compared to the software being used today. This length of time gives hackers plenty of opportunities to exploit vulnerabilities.
What can be done to minimize the risk of outdated medical device software?
The first step in minimizing the risk of outdated medical device software is to compile a list of all of the medical devices that are currently in operation. This list will act as an electronic inventory management system. Important information to include on this list is:
- Device manufacturer
- Model number or version
- Purchase date
- Expiration date
- Software components being used
- Operating systems
- SBOM (software bill of materials) - In the FDA’s recent guidance for cybersecurity, they recommend that manufacturers build in the ability for devices to be updated and also that the manufacturer develop an SBOM so it’s much easier to track software developers, including third parties.
Getting this list together will give you an idea of any potential cyber risks and allow you to prioritize the next steps to solve any issues.
One more thing to consider is to train employees who are using the software and devices about how to spot potential security threats, including internal threats from employees. Sometimes these threats are known by the developers or manufacturers, but the healthcare organizations remain unaware.
Cybersecurity threats to medical devices continues to be a big problem for healthcare organizations. ECRI, a nonprofit that evaluates medical devices for safety and efficacy, even selected cybersecurity as the top medtech hazard for 2022.
If you are currently using medical devices with outdated software, it’s definitely worth your time to look into how to get the software updated. If the device is no longer supported, you may need to look to an experienced developer in the healthcare industry.
If you have any questions or need help with a solution, just use the button below to contact our team.
